Creating a high-availability network requires careful planning to guarantee continuous service despite failures. You need to select the right topology, like mesh or hybrid, that offers multiple paths for data transfer. Implementing failover protocols such as STP and VRRP helps detect issues and reroute traffic automatically. Understanding how these components work together can make the difference between a resilient network and one prone to downtime—so, considering these options carefully is essential.
Key Takeaways
- Implement a hybrid network topology combining mesh and star structures for optimal redundancy and fault isolation.
- Utilize failover protocols like STP and VRRP to enable automatic rerouting and device failover.
- Incorporate multiple redundant links between critical network devices to prevent single points of failure.
- Design the network with centralized management for quick detection and containment of faults.
- Regularly test and update failover mechanisms to ensure seamless high-availability operations.

Have you ever wondered how networks stay online even when components fail? The secret lies in designing a redundant network with robust architecture and smart protocols. At the core of this resilience is your network topology, which determines how devices connect and communicate. Choosing the right topology—such as a mesh, star, or hybrid—can profoundly enhance fault tolerance. For instance, a mesh topology provides multiple pathways for data, so if one link drops, traffic seamlessly reroutes through alternate routes. Similarly, a star topology centralizes connections, making it easier to isolate failures and prevent them from cascading. Your goal is to create a network that can withstand hardware failures without disrupting services, and selecting an appropriate topology is the first step toward that.
Beyond the physical design, failover protocols play a critical role in maintaining high availability. These protocols automatically detect failures and switch operations to backup systems or alternate links without manual intervention. For example, Spanning Tree Protocol (STP) prevents loops in network topologies and ensures a single active path, but when a link fails, it recalculates and activates a backup path. Virtual Router Redundancy Protocol (VRRP) enables multiple routers to work together, so if your primary router goes down, a secondary takes over instantly, keeping traffic flowing smoothly. These failover protocols work behind the scenes, constantly monitoring network health and swiftly redirecting traffic as needed. Incorporating redundant network design is essential to maximize fault tolerance and ensure continuous operation.

NETGEAR 5-Port Gigabit Ethernet Unmanaged Essentials Switch (GS305) – Home Network Hub, Office Ethernet Splitter, Plug-and-Play, Silent Operation, Desktop or Wall Mount
5 Gigabit Ethernet ports
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Does Redundancy Impact Network Latency?
Redundancy can increase network latency due to additional pathways and equipment, creating latency trade-offs between reliability and speed. However, with redundancy optimization, you can minimize this impact by strategically placing backup links and equipment to ensure quick failover without significant delay. Properly balancing redundancy and latency allows your network to stay highly available while maintaining acceptable performance levels, so you get both reliability and efficiency.
What Are the Cost Implications of High Redundancy?
You might think high redundancy costs are a small price to pay, but they actually involve significant cost trade-offs. While redundancy benefits include increased reliability and minimized downtime, you’ll face higher expenses for extra hardware, maintenance, and complex configurations. Ironically, these costs can outweigh the savings from avoided outages, making it essential to carefully balance the benefits of high availability against the real financial impact on your network budget.
How to Prioritize Critical Network Paths During Failure?
You should identify your critical network paths first, then implement failover strategies like automatic rerouting and load balancing to guarantee these paths stay active during failures. Prioritize traffic based on importance, so essential services always have backup routes. Regularly test failover processes to confirm seamless changeover. By doing this, you minimize downtime and maintain high availability, even when parts of your network experience outages.
What Are Common Pitfalls in Redundant Network Implementation?
Like trying to find a floppy disk in a cloud, you might overlook common pitfalls. You risk creating single points of failure if you don’t properly eliminate them. Misconfiguration risks are high if you don’t thoroughly test your redundancy setup. Overlooking proper network segmentation or ignoring failover testing can cause unexpected outages. Confirm you plan for all scenarios, double-check configurations, and avoid assuming that redundancy alone guarantees high availability.
How Does Redundancy Affect Network Management Complexity?
Redundancy increases network management complexity because you need to coordinate backup switches and implement load balancing effectively. You’ll have to monitor multiple devices, configure failover protocols, and guarantee seamless traffic distribution. This demands more oversight, troubleshooting, and regular testing. While redundancy boosts reliability, it also means you must stay vigilant in managing backup switches and fine-tuning load balancing to prevent issues and maintain high availability.

Sonicwall TZ80 High Availability Model – Network Security Appliance (03-SSC-2749) | Not a Standalone Unit | Secondary Device for Reliable, Continuous Connection
High Availability units deliver seamless failover, network resilience, and business continuity by pairing with a primary firewall. Requires…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
By choosing robust topologies like mesh or hybrid structures and implementing failover protocols such as STP and VRRP, you create a highly available network that can withstand hardware failures. Visualizing this setup as a safety net illustrates how multiple pathways and automatic rerouting maintain your network running smoothly. This approach guarantees continuous connectivity, minimizes downtime, and supports your enterprise’s resilience, proving that strategic design and reliable protocols truly make your network fault-tolerant.

The Essential Guide to Serial ATA and SATA Express
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
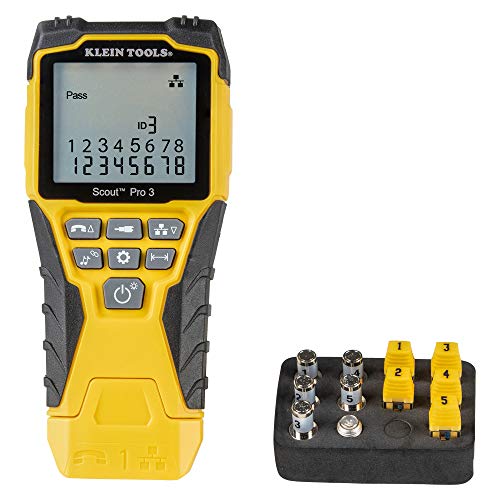
Klein Tools VDV501-851 Cable Tester Kit with Scout Pro 3 for Ethernet / Data, Coax / Video and Phone Cables, 5 Locator Remotes
VERSATILE CABLE TESTING: Cable tester tests voice (RJ11/12), data (RJ45), and video (coax F-connector) terminated cables, providing clear…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.