Imagine a network as a bustling city; without proper zoning, chaos can quickly ensue. Network segmentation and VLANs act as the city’s zoning laws, organizing traffic and enhancing security. By dividing your network into smaller, manageable parts, you control data flow and reduce risks. But how exactly do VLANs create these virtual boundaries, and what benefits do they bring? Exploring these concepts can help you build a more secure and efficient infrastructure.
Key Takeaways
- Network segmentation divides a network into isolated zones to improve security and limit threat spread.
- VLANs are logical groupings of devices that create virtual networks within physical infrastructure.
- VLAN configuration involves assigning switch ports or access points to specific VLANs for proper segmentation.
- Inter-VLAN routing enables controlled communication between VLANs while maintaining security boundaries.
- Effective segmentation and VLAN management enhance network security, control, and resource manageability.

Network segmentation and VLANs are fundamental tools for improving security, performance, and manageability in modern networks. When you implement network segmentation, you’re essentially dividing your network into smaller, isolated sections. This process enhances network security because it limits the spread of threats, such as malware or unauthorized access, by preventing them from moving freely across all parts of your network. By segmenting your network, you create distinct zones, each with its own security policies and controls, which allows you to isolate sensitive data and critical systems from less secure areas.
Network segmentation creates isolated zones, enhancing security by limiting threat movement across your network.
VLANs, or Virtual Local Area Networks, play a pivotal role in achieving effective network segmentation. They enable you to logically group devices based on function, department, or security level, regardless of their physical location. Setting up VLAN configuration involves assigning switch ports or wireless access points to specific VLANs, effectively creating separate virtual networks within the same physical infrastructure. This approach simplifies management because you can control traffic flow, security policies, and access permissions at the VLAN level, rather than configuring each device individually.
One key benefit of VLANs is network isolation. By isolating different groups of devices into separate VLANs, you prevent unnecessary traffic from reaching unintended recipients. For example, you can create a VLAN for finance, another for HR, and a third for guest Wi-Fi. This separation ensures that sensitive financial data remains protected from general network traffic and that guests cannot access internal resources. Proper VLAN configuration is essential for maintaining this isolation; it involves carefully planning which devices belong to each VLAN and configuring switches and routers accordingly. Additionally, implementing inter-VLAN routing is necessary to facilitate controlled communication between VLANs while maintaining security boundaries.
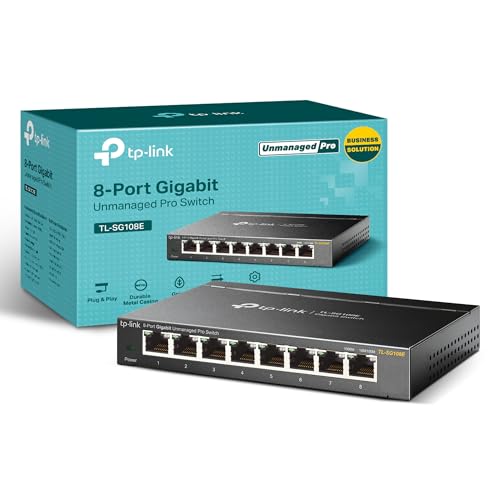
TP-Link 8 Port Gigabit Switch | Easy Smart Managed | Plug & Play | Desktop/Wall-Mount | Sturdy Metal w/ Shielded Ports | Support QoS, Vlan, IGMP and LAG (TL-SG108E)
𝟴 𝗚𝗶𝗴𝗮𝗯𝗶𝘁 𝗘𝘁𝗵𝗲𝗿𝗻𝗲𝘁 𝗣𝗼𝗿𝘁𝘀: expand your network with 8 high-speed ethernet ports
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Does Network Segmentation Impact Overall Network Performance?
Network segmentation improves your overall network performance by enhancing network efficiency and traffic optimization. When you segment your network, you reduce congestion by isolating traffic within specific segments, which prevents unnecessary data flow across the entire network. This targeted approach minimizes delays, boosts speed, and ensures smoother communication. As a result, your network becomes more responsive, reliable, and capable of handling higher loads without compromising performance.
Can VLANS Be Used in Wireless Networks Effectively?
Yes, wireless VLANs work effectively, much like dividing a busy airport into secure zones. You can create wireless VLANs to segment traffic and improve security, offering great VLAN flexibility. For example, you might separate guest Wi-Fi from internal staff networks, ensuring smooth performance and security. Using wireless VLANs, you’ll find your network more organized and responsive, especially in environments with diverse device types and user needs.
What Are Common Security Risks Associated With VLAN Misconfigurations?
VLAN misconfigurations can expose you to security risks like VLAN theft and misconfiguration vulnerabilities. If you don’t properly set up VLANs, attackers might access sensitive data or intercept network traffic. Misconfigured VLANs can also allow unauthorized devices to connect, increasing the chance of network breaches. Always review your VLAN settings carefully, enforce strong policies, and monitor network activity to minimize these vulnerabilities and protect your network.
How Do VLANS Interact With Network Firewalls and Security Policies?
You guarantee VLAN security by properly configuring firewall rules to control traffic between VLANs. Firewalls monitor and filter data as it moves across VLAN boundaries, enforcing security policies. You should set specific rules to restrict unauthorized access and prevent lateral movement. Regularly review and update these rules to adapt to emerging threats. Proper VLAN interaction with firewalls enhances your network’s overall security by isolating sensitive segments and controlling data flow.
What Are the Best Practices for Managing VLANS at Scale?
Did you know that organizations managing over 50 VLANs often see a 30% increase in network efficiency? To manage VLANs at scale, you should prioritize thorough VLAN planning and consistent IP address management. Automate VLAN provisioning where possible, document configurations meticulously, and implement centralized control tools. Regular audits help identify issues early, ensuring your VLANs remain organized, secure, and scalable as your network grows.

Polar Lights Star Trek USS Enterprise Refit 1:350 Scale Model Kit – Highly Detailed Sci-Fi Collectible with Interior Docking Bay
Authentic Design: Features precise details, including a highly detailed interior docking bay with shuttlecraft and work bees.
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
So, after all this, you might think that dividing networks with VLANs is a foolproof way to boost security. But remember, even the best-separated segments can be compromised if you overlook proper configuration or neglect monitoring. It’s almost ironic—creating barriers to protect your data can sometimes become a false sense of security. Ultimately, while VLANs simplify management, they’re not a magic shield; vigilance remains your last line of defense.

HOMELAB SECURITY AND PRIVACY HARDENING: Build a Secure Self-Hosted Infrastructure with Zero Trust Architecture. VPNs, Firewalls, Encryption, Network Segmentation, and Intrusion Detection
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

TRENDnet Gigabit Multi-WAN VPN Business Router, TWG-431BR, 5 x Gigabit Ports, 1 x Console Port, QoS, Inter-VLAN Routing, Dynamic Routing, Load-Balancing, High Availability, Online Firmware Updates
INTERFACE: 5 x Gigabit ports (Modes:4 WAN ports/1 LAN port or 1 WAN port/4 LAN ports), 1 x…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.









